Delegated bypass for push protection lets you define who can push commits containing secrets and adds an approval process for other contributors. See About delegated bypass for push protection.
To enable delegated bypass, create the teams or roles that will manage bypass requests. Alternatively, use fine-grained permissions for more granular control. See Using fine-grained permissions to control who can review and manage bypass requests.
Enabling delegated bypass for a repository
참고
If an organization or enterprise owner configures delegated bypass at the organization or enterprise level, the repository-level settings are disabled.
-
On GitHub, navigate to the main page of the repository.
-
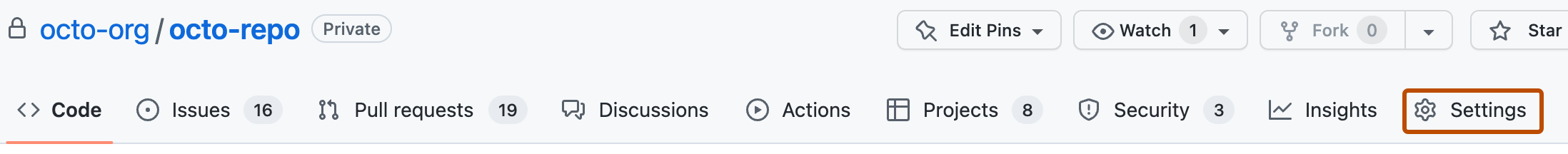
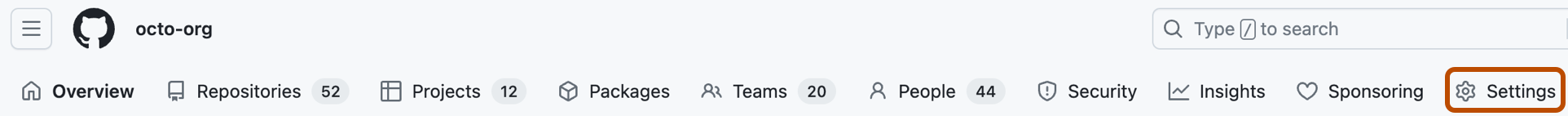
Under your repository name, click Settings. If you cannot see the "Settings" tab, select the dropdown menu, then click Settings.
-
In the "Security" section of the sidebar, click Advanced Security.
-
Under "Secret Protection," ensure that push protection is enabled for the repository.
-
Under "Push protection," to the right of "Who can bypass push protection for secret scanning," select the dropdown menu, then click Specific roles or teams.
-
Under "Bypass list," click Add role or team.
-
In the dialog box, select the roles and teams that you want to add to the bypass list, then click Add selected.
참고
You can't add secret teams to the bypass list.
Enabling delegated bypass for an organization
-
On GitHub, navigate to the main page of the organization.
-
Under your organization name, click Settings. If you cannot see the "Settings" tab, select the dropdown menu, then click Settings.
-
In the "Security" section of the sidebar, select the Advanced Security dropdown menu, then click Configurations.
-
Create a new custom security configuration, or edit an existing one. See Creating a custom security configuration.
-
When defining the custom security configuration, under "Secret scanning," ensure that "Push protection" is set to Enabled.
-
Under "Push protection," to the right of "Bypass privileges," select the dropdown menu, then click Specific actors.
-
Select the Select actors dropdown menu, then choose the actors you want to add to the bypass list.
참고
- You can't add secret teams to the bypass list.
- In addition to assigning bypass privileges to roles and teams, you can also grant individual organization members the ability to review and manage bypass requests using fine-grained permissions. See Using fine-grained permissions to control who can review and manage bypass requests.
-
Click Save configuration.
-
Apply the security configuration to repositories in your organization. See Applying a custom security configuration.
Using fine-grained permissions to control who can review and manage bypass requests
You can grant specific individuals or teams in your organization the ability to review and manage bypass requests using fine-grained permissions.
- Ensure that delegated bypass is enabled for the organization. For more information, follow steps 1-3 in Enabling delegated bypass for your organization and ensure you have saved and applied the security configuration to your selected repositories.
- Create (or edit) a custom organization role. For information on creating and editing custom roles, see Managing custom organization roles.
- When choosing which permissions to add to the custom role, select the "Review and manage secret scanning bypass requests" permission.
- Assign the custom role to individual members or teams in your organization. For more information on assigning custom roles, see Using organization roles.